This is a Custom Metasploit Auxiliary Module developed to perform post-exploitation reconnaissance on Azure Cloud Infrastructure. The module targets the Azure Instance Metadata Service (IMDS) to extract sensitive metadata about a Virtual Machine from an internal perspective.
- VM Identification: Virtual Machine Name & Unique Instance ID
- Network Infrastructure: Public & Private IP Addresses
- Geographical Data: Azure Region / Location
- System Specs: VM Size (SKU) & Operating System details
sudo gem install azure_mgmt_compute
sudo gem install azure_mgmt_resources# Navigate to the auxiliary modules directory
cd /usr/share/metasploit-framework/modules/auxiliary/
# Create a custom category folder
sudo mkdir cloudy
# Copy the module file
sudo cp azure_vm_enum.rb /usr/share/metasploit-framework/modules/auxiliary/cloudy/msfconsole
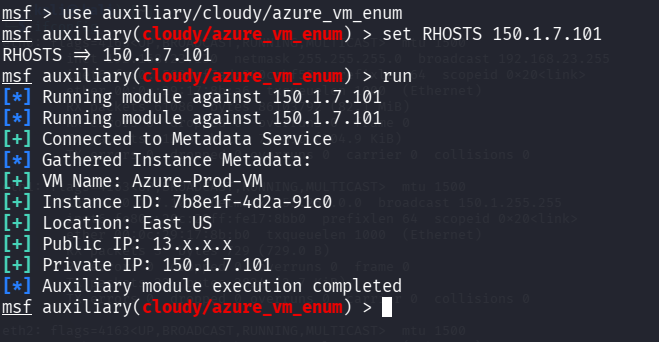
msf > reload_all# Select module
msf > use auxiliary/cloudy/azure_vm_enum
# Set target
msf6 auxiliary(cloudy/azure_vm_enum) > set RHOSTS <Target_IP>
# Run
msf auxiliary(cloudy/azure_vm_enum) > runNaeem Akmal BS Computer Science – University of Lahore
- GitHub: https://github.com/NaeemAkmal
- LinkedIn: https://www.linkedin.com/in/naeemakmal15/
This tool is for educational purposes and authorized testing only. Unauthorized use is illegal.