You signed in with another tab or window. Reload to refresh your session.You signed out in another tab or window. Reload to refresh your session.You switched accounts on another tab or window. Reload to refresh your session.Dismiss alert
Copy file name to clipboardExpand all lines: README.md
+47Lines changed: 47 additions & 0 deletions
Display the source diff
Display the rich diff
Original file line number
Diff line number
Diff line change
@@ -7,6 +7,15 @@ An anonymous proxy written in kotlin.
7
7
For a deeper architectural overview of how the modules and external libraries fit together,
8
8
see [docs/architecture.md](docs/architecture.md).
9
9
10
+
## Demo videos
11
+
12
+
Two short clips of the Android sample app in action (click to play on YouTube):
13
+
14
+
| Android demo | Android demo with Wireshark |
15
+
|:---:|:---:|
16
+
|[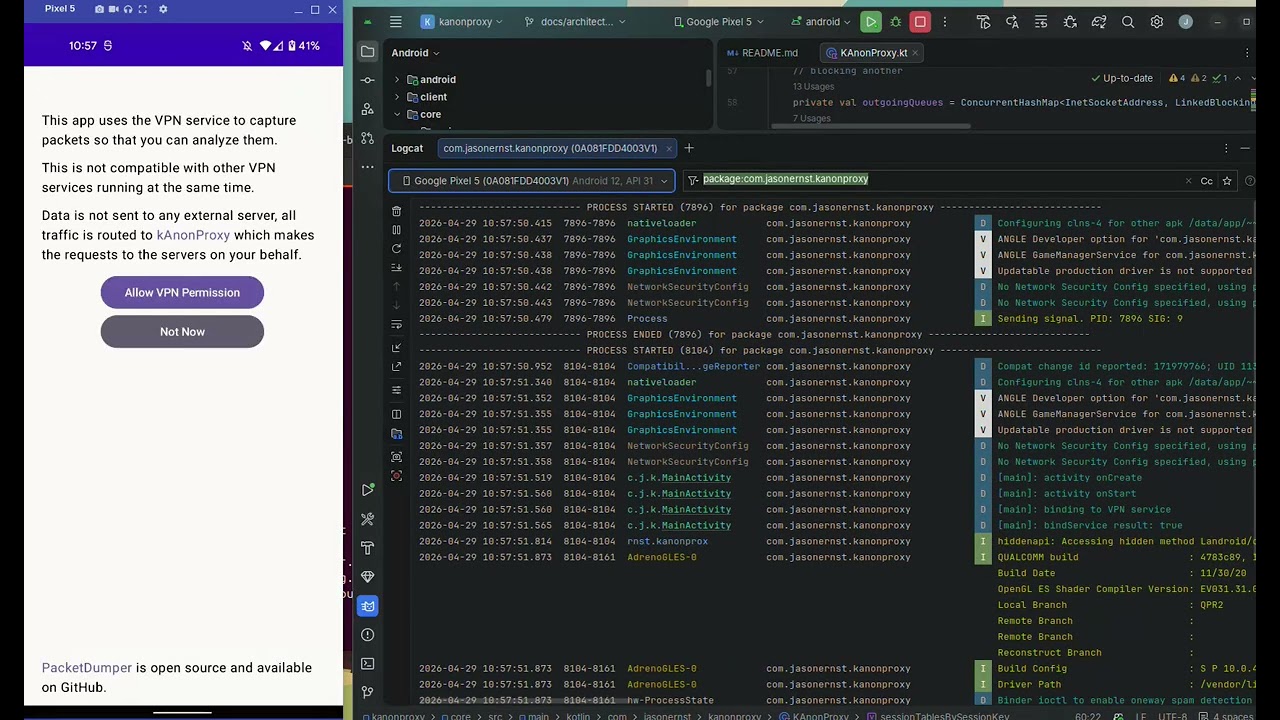](https://youtu.be/wlaYF5m-GBo)|[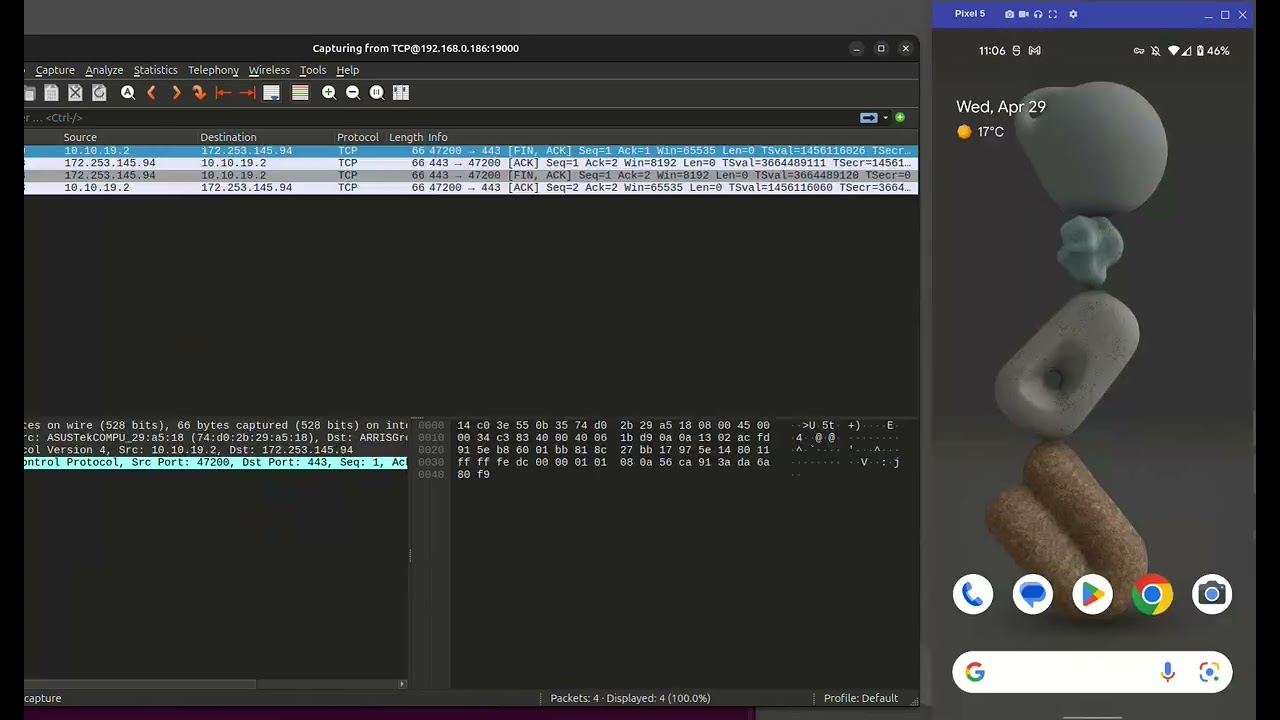](https://youtu.be/zhUrEmBCZSM)|
17
+
| The `android` module running as a VPN service and proxying traffic on a real device. | The same app with Wireshark attached to the in-app `PcapNgTcpServerPacketDumper`, watching packets go through the proxy live. |
18
+
10
19
## Modules
11
20
12
21
There are four modules in this project:
@@ -84,3 +93,41 @@ val response = kanonProxy.takeResponse()
84
93
```
85
94
86
95
There are more examples of usage in the [tests](core/src/test/kotlin/com/jasonernst/kanonproxy).
96
+
97
+
## Debugging with Wireshark
98
+
99
+
Both the reference server/client and the Android sample app embed a
100
+
[`PcapNgTcpServerPacketDumper`](https://github.com/compscidr/packetdumper) that can
101
+
expose a live pcap-ng stream over TCP. Wireshark attaches to it directly, no PCAP
102
+
files on disk:
103
+
104
+
```bash
105
+
wireshark -k -i TCP@<host>:<port>
106
+
```
107
+
108
+
`-k` starts capture immediately; `-i TCP@host:port` is Wireshark's pcap-ng-over-TCP
109
+
source. The host and port depend on where the dumper is running:
110
+
111
+
-**`LinuxProxyClient`** — listens on `PcapNgTcpServerPacketDumper.DEFAULT_PORT`
112
+
(`19000`) on localhost:
113
+
```bash
114
+
wireshark -k -i TCP@127.0.0.1:19000
115
+
```
116
+
117
+
-**`ProxyServer.main`** — listens on `PcapNgTcpServerPacketDumper.DEFAULT_PORT + 1`
118
+
(`19001`) on localhost, to avoid clashing with a co-located client:
119
+
```bash
120
+
wireshark -k -i TCP@127.0.0.1:19001
121
+
```
122
+
123
+
-**Android sample app** — the dumper is *not* started with the VPN; you have to
124
+
enable it from the app's UI (the Wireshark/pcap-server toggle, which calls
125
+
`startPcapServer()`). Once enabled it listens on the phone's Wi-Fi interface, so
126
+
`127.0.0.1` will not work from your computer. Use the **phone's Wi-Fi IP**, and
127
+
make sure the phone and the computer running Wireshark are on the **same subnet**
128
+
(and that no AP isolation / firewall blocks port `19000`):
129
+
```bash
130
+
wireshark -k -i TCP@<phone-wifi-ip>:19000 # e.g. TCP@192.168.1.42:19000
131
+
```
132
+
You can find the phone's Wi-Fi IP under Settings → About phone → Status, or
0 commit comments