You signed in with another tab or window. Reload to refresh your session.You signed out in another tab or window. Reload to refresh your session.You switched accounts on another tab or window. Reload to refresh your session.Dismiss alert
@@ -164,21 +170,73 @@ When the pipeline is manually triggered or runs on a schedule, the results are u
164
170
| debug | Enable debugging | Optional | `false` |
165
171
166
172
## Policy Checks
167
-
The SCANOSS Code Scan Task includes two configurable policies:
173
+
The SCANOSS Code Scan Task includes three configurable policies:
168
174
169
-
1. Copyleft: This policy checks if any component or code snippet is associated with a copyleft license. If such a
175
+
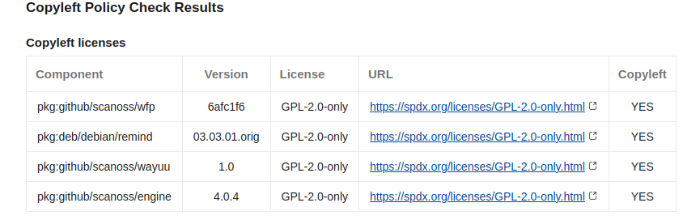
1. **Copyleft**: This policy checks if any component or code snippet is associated with a copyleft license. If such a
170
176
license is detected, the pull request (PR) is rejected. The default list of Copyleft licenses is defined in the following [file](https://github.com/scanoss/ado-code-scan/blob/1218c4fe2dcda5f807b505e271096b1ec0afd8a9/codescantask/utils/license.utils.ts#L4).
171
177
172
-
2. Undeclared: This policy compares the components detected in the repository against those declared in the scanoss.json
178
+
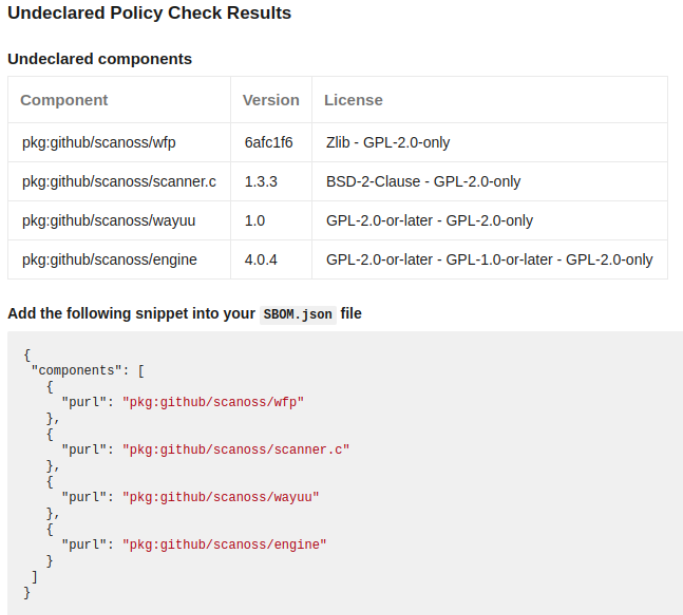
2. **Undeclared**: This policy compares the components detected in the repository against those declared in the scanoss.json
173
179
file. If there are undeclared components, the PR is rejected.
174
180
181
+
3. **Dependency Track** (deptrack): This policy integrates with a Dependency Track server to check for policy violations including security vulnerabilities, license violations, and compliance issues as configured in your Dependency Track policies. The policy check queries an existing Dependency Track project for violations and reports them in the pipeline.
182
+
183
+
**Requirements:**
184
+
- Dependency Track server URL and API key
185
+
- Either a project UUID or project name/version
186
+
- The policy runs even if SBOM upload is disabled, but will show warnings if checking against potentially stale data
187
+
188
+
**Configuration Example:**
189
+
```yaml
190
+
inputs:
191
+
policies: copyleft,undeclared,deptrack
192
+
depTrackEnabled: true
193
+
depTrackUrl: 'https://deptrack.example.com'
194
+
depTrackApikey: $(DEPTRACK_API_KEY)
195
+
depTrackProjectName: 'my-project'
196
+
depTrackProjectVersion: '1.0.0'
197
+
```
198
+
175
199
Additionally, if it is a Pull Request, a comment with a summary of the report will be automatically generated.
176
200
177
201
178
202
179
203
180
204
181
205
206
+
## Dependency Track Integration
207
+
208
+
The SCANOSS Code Scan Task integrates with Dependency Track to provide enhanced vulnerability tracking and policy enforcement. This integration consists of two main features:
209
+
210
+
### 1. SBOM Upload Status Check
211
+
212
+
When `depTrackEnabled` is set to `true`, the task will automatically upload a CycloneDX SBOM to your Dependency Track server and report the upload status as a separate PR status check. This status check provides:
213
+
214
+
- **Success/Failure status**: Visual indicator of whether the SBOM was successfully uploaded
215
+
- **Upload details**: Information about the uploaded SBOM including:
216
+
- Project name and version
217
+
- Number of components analyzed
218
+
- File size and upload time
219
+
- Direct link to the project in Dependency Track
220
+
- **PR comments**: Detailed success or failure messages posted as PR comments
221
+
- **Troubleshooting guidance**: If upload fails, helpful error messages with configuration tips
222
+
223
+
**Note**: The SBOM upload status check runs independently from the policy checks. You can enable SBOM upload without enabling the Dependency Track policy check.
224
+
225
+
**Configuration Example:**
226
+
```yaml
227
+
inputs:
228
+
depTrackEnabled: true
229
+
depTrackUrl: 'https://deptrack.example.com'
230
+
depTrackApikey: $(DEPTRACK_API_KEY)
231
+
depTrackProjectName: 'my-project'
232
+
depTrackProjectVersion: '1.0.0'
233
+
```
234
+
235
+
### 2. Dependency Track Policy Check
236
+
237
+
The Dependency Track policy check (enabled by adding `deptrack` to the `policies` parameter) queries your Dependency Track server for policy violations and fails the build if violations are found. This is separate from the upload functionality and can be used independently.
238
+
239
+
See the **Policy Checks** section above for detailed information about the Dependency Track policy check.
182
240
183
241
## Artifacts
184
242
The scan results and policy check outcomes are uploaded to the artifacts folder of the specific run of the pipeline.
0 commit comments